We need to talk about a dirty not-so-little secret in the bot mitigation industry.
Enterprising actors in the underground bot economy are creating and selling APIs that “solve” or bypass specific bot management technologies. Now it’s easier than ever for mainstream bot operators to scrape content, take over accounts, hoard inventory, and commit other forms of automated fraud against organisations using legacy bot management solutions.
The resulting asymmetric cost differential between attackers and defenders is astronomical. For less than $500 per month, attackers can purchase “Solver” bots, APIs, and services to make a profit. Contrast that with organisations paying tens of thousands per month for *leading* bot management solutions – the same solutions that Solver Services circumvent. Worse, those monthly platform fees don’t cover integration costs, ongoing professional services, and constant maintenance. The cruel truth is that the inefficacy of these solutions shifts the burden of fighting bots back to the customers, and the balance of power strongly favors the attackers.
Whether or not established bot mitigation vendors are aware of this problem, they are not actively solving it – and therefore, their customers’ data, brand reputation, and revenue are at stake.
Background: How Bot Mitigation Solutions Work
There are two primary types of detection that a bot mitigation vendor can have: client-side detection and server-side detection.
- Client-side detection involves collecting data from a browser or mobile device and using that data to classify a session, which usually gives the client a “Token.” These Tokens are like tickets to access protected customers’ websites and mobile APIs. Telemetry is also an important term to understand, which refers to data collected from the client.
- Server-side detection involves looking at the patterns in requests to the protected customers’ websites. Server-side detection techniques aim to distinguish anomalies from “normal” traffic based on these patterns. For example, it’s normal user behaviour to perform a login attempt a few times, but it’s not normal for a user to perform one hundred login attempts.
Attackers go to great lengths to masquerade their engineered requests and look like they come from real users. They will commonly patch browser requests and then proxy them through hundreds, if not thousands, of legitimate data center and residential IP addresses. Some bot mitigation vendors only employ server-side detection, making them especially vulnerable to distributed attacks that mimic human traffic patterns.
*We strongly recommend selecting a vendor that uses robust client-side AND server-side detection techniques. Server-side only solutions are not quick enough to effectively detect and respond to threats because they lack client-side context.
How Attackers Evade Detection Via Solver Services
TL;DR: Attackers are now using low-cost Solver bots, APIs, and services to quickly and easily bypass high-cost bot mitigation solutions.
Here is a breakdown of Solver Services and Bots, along with an explanation of the various bot operators’ levels of ability:
- Solver Services: built and maintained by the innermost level and most sophisticated attackers.
- Request Bots: created by bot builders that use the Solver APIs to write their own custom bots. These bot operators are not as sophisticated, but still have the ability to code.
- All-in-One (AIO) Bots: all-in-one products that wrap all the above into a neat package with an elegant UI. AIO Bots are provided to mainstream actors that do not need tech skills.
These sophisticated attackers who are able to reverse engineer a bot mitigation vendor’s defence develop a “Solver Service” that extracts the bot mitigation vendor’s scripts and telemetry model. As a result, the Service generates realistic – but fake – data that it will submit to the defence system, fooling the bot mitigation solution into granting it a valid Token.
Once attackers get the valid Token, they expose an API for the Service and subsequently sell it to mainstream attackers. Mainstream attackers then use this bypass service to obtain valid Tokens without doing any of the heavy lifting or reverse engineering.
These attackers are very entrepreneurial, aren’t they?
How a Solver Service Works
In the diagram below, we further explain the steps of how a Solver Service works in the bot underground.
Step 1 – Publish Solver Bot/API
- A sophisticated attacker that we’ll call a Maintainer builds and publishes a Solver Bot/API.
Step 2 – Farm Tokens
- A mainstream bot builder purchases access to a Solver API Service maintained by the Maintainer.
- The mainstream bot builder writes a simple script to call the API for new Tokens and temporarily stores them for Step 2.
Step 3 – Use Tokens to Bypass the Bot Defence System
- The mainstream bot builder writes another script that performs individual requests required for their attack. For example: log in, browse for a particular shoe, add hundreds to the cart, and purchase the shoes.
- Each request they make uses a new Token. This makes it more difficult for the bot mitigation vendor’s rate-limiting or server-side machine learning models to detect the automated attack.
Unpacking A Real Example
All-in-One (AIO) Bots are used to target hype-release products, specifically in the apparel, electronics, and gaming industry. For example, a hot product in this space is in short supply due to chip shortages and other supply chain issues.
AIO developers are focused exclusively on building out a product to maximize their customer’s chances of securing products in these limited-release drops. Because each retailer uses a different set of controls to detect and block bots, AIO developers need to maintain multiple versions of their service.
To reduce the development effort to build and maintain these versions, AIO developers outsource the reverse engineering and token generation process to a Solver Bot. This allows them to cover more retailers, be more responsive to changes from bot mitigation vendors – and ultimately increase their customer satisfaction.
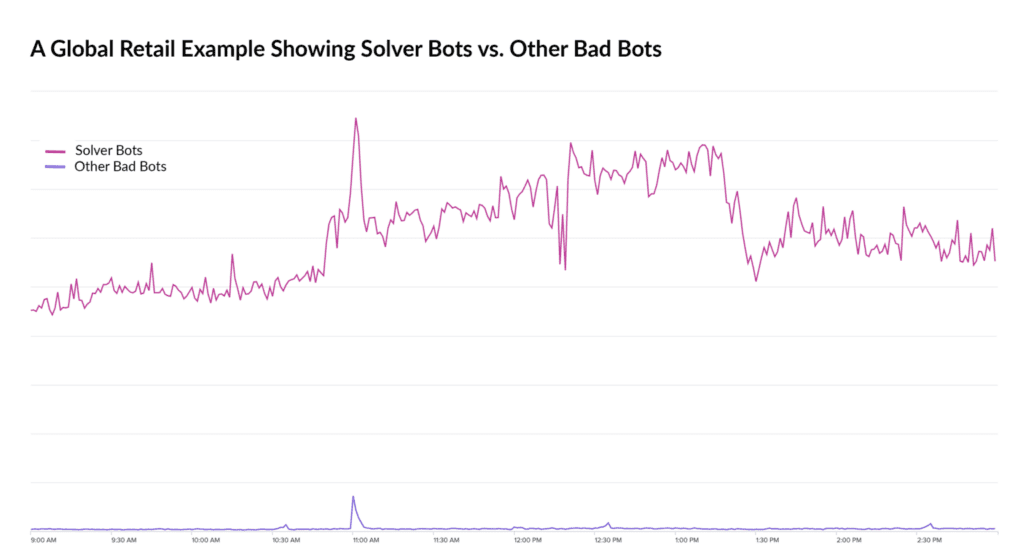
Example of a global retailer’s bad bot traffic over the course of several hours. Throughout the entire period, 95 – 99% of the total bad bot requests were from Solver APIs, whereas the requests from other types of bad bots such as those from headless browsers made up the remainder.
Motivation: It All Boils Down to Economics
Financially motivated bad actors will capitalize on opportunities to make the most money in the simplest way possible. These Solver Services are a game changer for not only mainstream attackers, but even more so the Maintainers of these Solver Services.
Solver Services vastly lower the barrier to entry for launching an automated attack, enabling mainstream attackers to more easily get their primary job done – which includes bagging hot, limited-edition sneakers and other hype-release items like NFTs. Threat actors can also use Solver Services to perform more insidious attacks, like committing online fraud. In fact, our Threat Intelligence Researchers have noticed an uptick in attackers leveraging these Solver Services to conduct Account Takeover (ATO) attacks.
The Maintainer of the Solver Service, on the other hand, benefits from a reliable revenue stream from tens to thousands of “customer” subscriptions. Each Solver Service typically charges based on usage. The price varies depending on the bot mitigation vendor and how difficult it is for the Maintainer to reverse engineer the vendor’s defence and maintain the service. Some of these Maintainers earn upwards of hundreds of thousands to millions of U.S. dollars per year, which gives Maintainers a significant incentive to keep the service working by retooling against the latest improvements.
Are Your Applications Susceptible to Solver Services?
Automation works best for repeatable steps that don’t change, so the bot mitigation vendors that are most vulnerable to these Solver Services are those that don’t change very often.
Deploying bot mitigation technology in and of itself isn’t going to take away adversaries’ motivation that make automated attacks viable. The only way to undermine their motivation is to disrupt the economics by making it so immensely difficult and time-consuming to reverse engineer and retool that it’s unprofitable, forcing bot operators to move on to other targets.
This is easier said than done, as many bot mitigation vendors on the market are not doing this sufficiently.
What it really takes to de-motivate adversaries:
-
Black-box detection: Obfuscate client-side detection so attackers can’t reverse-engineer how the bot mitigation works.
-
Dynamic, unpredictable defences: Continuously randomize protections to make it nearly impossible to automate bypasses at scale.
-
Think like an attacker: Stay ahead by constantly examining the threat landscape from the adversary’s perspective – fueling product innovation grounded in real-world tactics.
If your bot mitigation vendor isn’t taking all of these steps, you may be susceptible to the detrimental impact of Solver Services.
But wait – why wouldn’t a bot mitigation provider be doing anything about this? To be honest, we don’t really know the answer. When there’s a zero-day vulnerability, such as the recent open source zero-day vulnerabilities Spring4Shell and Log4j, security professionals rush to patch it – but when there’s a bot detection bypass available, security providers aren’t putting the same accountability on themselves to fix it. We find this to be unacceptable.
Defence in Depth: The Kasada Difference
Our view is that innovations like Solver Services actually up the ante for bot mitigation vendors to step up and build better products. Fortunately, this is something that Kasada has been focused on for years. We’re confident that we’ve released more defence techniques to address this problem than any other vendor in the market since long-lasting efficacy is our primary goal to accurately and effectively protect our customers.
Kasada’s approach randomizes defence and employs strong obfuscation in all elements of our platform. This is true anti-automation because the steps are always changing, which maximizes the difficulty for attackers to reverse engineer the solution. Each time they think they have the right approach to bypass, the defence changes, and their approach breaks. Additionally, our security engineers are constantly on the front lines fighting bots, innovating, and ensuring that we’re safeguarding our customers’ applications to the best of our ability.
The outcome is a highly effective defence for our customers – without the need for silly CAPTCHAs that interrupt a user’s experience and are easy to bypass as well.
Simply put, Kasada stops the bot attacks others can’t. See Kasada in action by requesting a demo.



