Want a PS5 for Christmas? Good Luck
It’s evident that “Grinch” bots have stolen Christmas this year… again. Over the past month, there have been numerous articles about how bots are being used to ruin shopping lists for many boys and girls that have been nice this year.
Whether the PlayStation 5, Xbox Series X, or other hot items with demand exceeding supply, hoarding and flipping enabled by automated bot purchases have become all too common. An estimated $30 million in profits have already been made this holiday season by bot operators reselling electronic consoles on auction sites such as eBay and Craigslist.
Most retailers are acting with the best intentions and genuinely care about putting their in-demand merchandise into the hands of their most loyal customers, not scalpers. Many are taking aggressive measures by tuning their bot mitigation rules in an attempt to stay ahead of the myriad of constantly changing sophisticated bots invading their website. Doing so helps protect their brand by satisfying shoppers and also has revenue implications as satisfied customers come back to buy games, accessories, and other merchandise that increase the total lifetime value of a customer. They’re also making attempts to cancel orders that are believed to be purchased using bots – but how do you know for sure which orders weren’t legit?
The Long-Tail of Bot Operators
More recently, the narrative has shifted away from the large, financially motivated groups that sought a big initial payoff to the long-tail of DIYers that want merchandise for themselves, or as a small side-hustle, once goods are restocked. These folks seek-out easily accessible bots to help them compete for inventory on their own. There are a variety of ways for such DIYers to gain access to Grinch bots and knowledge, such as downloading free browser plugins or joining inexpensive Cook Groups.
It is this long-tail of bot operators that have made defending against Grinch bots even more challenging. The democratization of bot networks, designed with a particular purpose in mind, coupled with the collective knowledge shared within communities of motivated, intelligent people.
If you think these DIY bots couldn’t be as sophisticated as those used by the larger, financially motivated groups – you’d be wrong. Retailers now have to contend with thousands of individuals active in online communities and their rapidly evolving bots, who are all trying to work their way through a retailer’s online defenses.
The Anatomy of a Grinch Bot
I downloaded one of these bots myself to gain an appreciation of what retailers are contending with this holiday season. It didn’t take me long to find a Grinch bot to use. In fact, there were hundreds of options to choose from online. With just my laptop, I directed this bot for two minutes against a product item on our own retail demo site. In a mere two minutes of running this bot, here is what I observed:
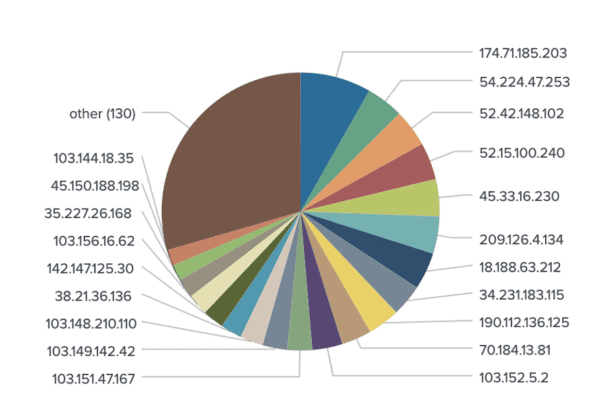
- Geographically Distributed IP Addresses – A total of 150 different IP addresses – only one of which was used to issue a request more than once. We later learned that it would take several hours before any of the IP addresses were reused
- Legitimate-Looking User Agents – In the following few minutes, roughly 518 unique user agents were generated and used. The vast majority of these agents presented themselves as legitimate, modern devices able to mask their true identity by appearing as normal.
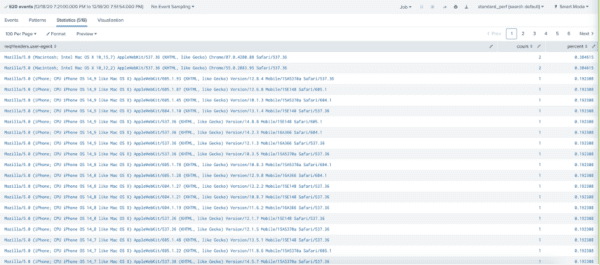
The rotation of user agents, coupled with the rotation of proxies, creates a nearly unrecognizable, invisible effect for detection. As a result, bot requests are able to fly under the radar of most bot mitigation tools and carry-out their intended purpose before their intent is discovered. Thus, attempts to detect and manage these bots – such as IP blocking, rate controls, device fingerprinting, and CAPTCHA – remain ineffective.
What’s a CISO to Do?
This basic example of a single, easy-to-access Grinch bot demonstrates the enormous challenge that exists within security teams to keep up with the evolving bad bot landscape in retail and most other industries.
The approach to mitigating sophisticated bots needs to be revised with more modern techniques. The current de facto approach requires letting legitimate requests through, identifying suspicious behavior, and only then stopping them from further action. By then it’s typically too late to avert inventory hoarding, web scraping, and other automated attacks.
Instead of looking for suspicious behavior after letting requests in, what if a zero-trust philosophy was taken such that all requests are assumed guilty until proven innocent? This is the approach Kasada takes with its bot mitigation.
Rather than blindly accepting requests from unknown sources, Kasada expects every request to prove that it’s from a legitimate source that’s controlled by a human. This means it can block bots that have never been seen before, or those unique to a particular organization, from the very first request. All without having to constantly tune and add rules based on what’s been learned from the past. We do this with a client-side interrogation process that detects the immutable evidence bots leave whenever they interact with websites, mobile apps, and APIs — despite their best efforts to mimic human behavior. Retooling attempts are deterred by frustrating, deceiving, and making attacks too costly to conduct for fraudsters.
Request a Threat Briefing
Request a no-obligation threat briefing to learn how to accurately stop bot operators who use malicious automation to work around your existing web and mobile defenses. We will demonstrate our unique approach to stopping sophisticated bot attacks that others can’t.



