In today’s digital landscape, the importance of API security cannot be overstated. With the rise of API breaches and the sensitive data at stake, organizations must implement robust security measures to protect their APIs. But what are API security best practices, and how can businesses defend their APIs against automated threats? Solutions like Kasada’s bot management solution can offer API protection to help safeguard your APIs as well as follow these API security best practices.
Key Takeaways
- API Security is a comprehensive security protocol for protecting against cyberattacks and unauthorized use.
- Common API vulnerabilities can be prevented with strong authentication, encryption, data validation, and monitoring/logging.
- Kasada API Protection offers advanced features to protect APIs from automated threats while providing key benefits such as increased customer trust.
What are Application Programming Interfaces? (APIs)

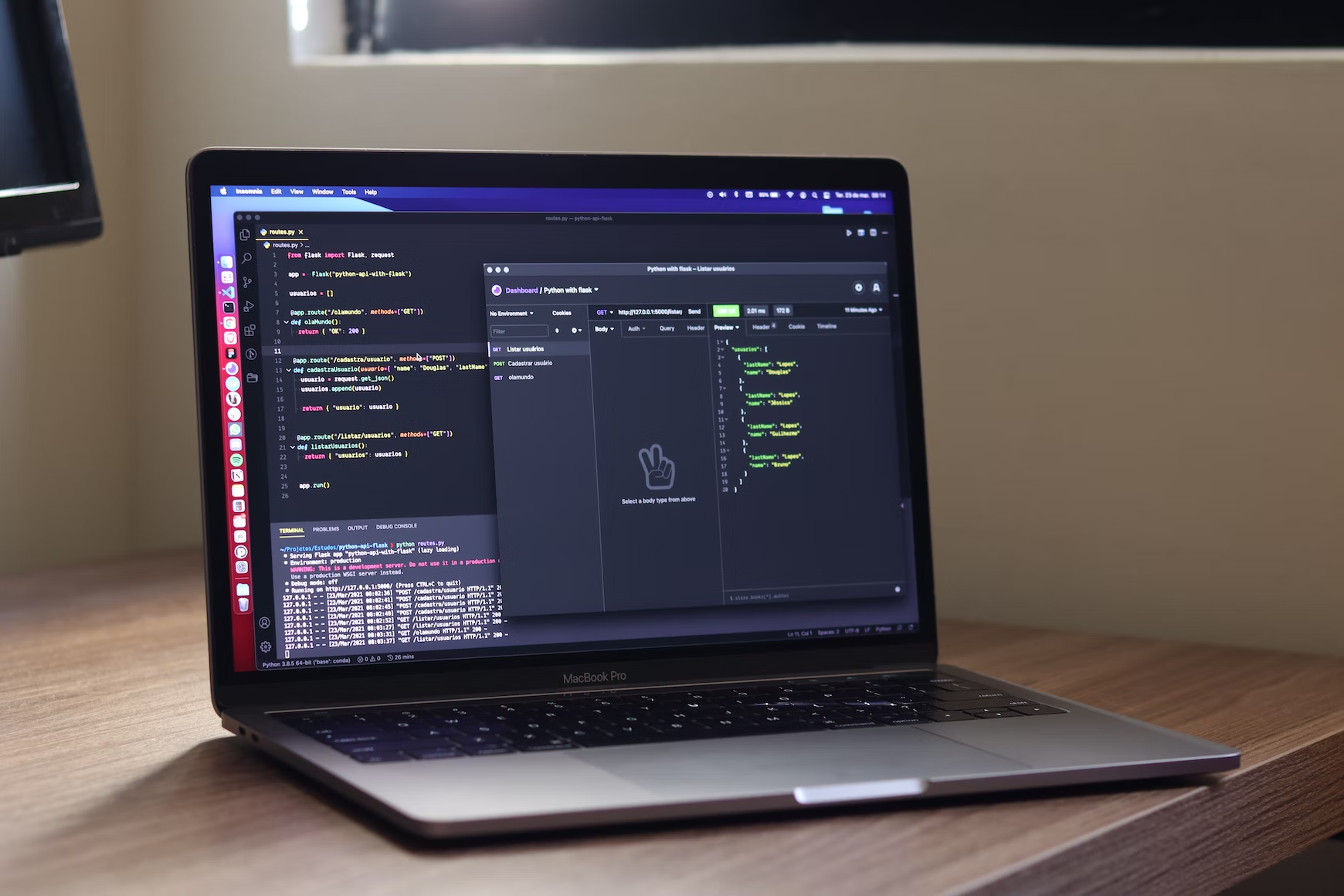
APIs, or Application Programming Interfaces, act as intermediaries that facilitate communication and data sharing between applications. As the digital world evolves, the significance of APIs in modern software development has grown exponentially. Cloud computing has become commonplace, and monolithic applications have been replaced by microservices. APIs play a crucial role in everyday technology, with examples such as:
- Weather snippets
- Log-in using XYZ
- PayPal payment integration
- Google Maps
- Travel booking
- E-commerce
However, the widespread use of APIs also exposes organizations to security risks. Currently, there are over 24,000 public APIs that require API keys and are utilized by millions of developers and hundreds of thousands of organizations worldwide. These APIs often handle sensitive data, making them attractive targets for attackers. Ensuring the security of APIs is of utmost importance to protect valuable information and maintain the integrity of the systems they support.
What is API Security?
The importance of API security cannot be overstated. It focuses on protecting against cyberattacks and unauthorized use of an API. Appropriate security controls can help organizations maintain the confidentiality, integrity, and availability of data handled by APIs. API security measures must be robust enough to defend against various types of attacks, such as stolen authentication, man-in-the-middle attacks, and code injections, among others.
Comprehensive security measures are essential to prevent unauthorized access to sensitive data and protect against data breaches. Best practices for API security, or API security best practices, include API security testing, which involves:
- Strong authentication and authorization mechanisms
- Encryption
- Data validation
- Monitoring
- Logging
Adhering to these best practices enables businesses to protect their APIs and preserve user and customer trust.
API Attacks
API attacks can take various forms, including:
- Stolen authentication: when an unauthorized individual obtains an authentication token, API key, or password of an authorized user and uses it to access resources with malicious intent.
- Man-in-the-middle attacks: where an attacker intercepts communication between two parties and can modify or steal data.
- Code injections: when an attacker injects malicious code into an API request to exploit vulnerabilities in the system.
- Denial-of-service (DoS) attacks: where an attacker overwhelms an API with a high volume of requests, causing it to become unresponsive or crash.
A notable example of a DoS attack on a web API is the 2017 attack on the FCC website, which utilized commercial cloud services to send a large number of API requests to its commenting system, ultimately causing the website to crash.
API firewalls can:
- Monitor and analyze API traffic
- Collect and analyze logs
- Provide insights into API usage and potential security issues to detect potential security incidents
Automated attacks on APIs can be hard to stop, since bots have the capability of imitating genuine human behavior, thereby evading detection. Nonetheless, there are measures to protect against such attacks. One way to reduce these risks is to implement authentication mechanisms that provide strong security.
In addition to stolen authentication and DoS attacks, code injections pose a significant threat to API security. Code injections occur when an attacker attempts to inject malicious scripts into an application’s server via an API request, with the intent of:
- Exploiting broken object-level authorization
- Exposing or deleting data
- Planting false information
- Damaging the application’s internals
Insights into API usage, potential security risks, and enhanced API security can be obtained through monitoring and analyzing API traffic.
The Role Bots Play in API Attacks
Like any use of malicious automation during any type of attack, bots are leveraged for their blend of ease of use, sophistication, and cost-effectiveness. Bots allow adversaries to launch API attacks at scale. Carrying out malicious actions far faster than a human could. If APIs are not protected against automation it leaves them vulnerable to attackers’ favorite tool.
The Rise of API Breaches
Over the past five years, there has been a steady increase in the number of API breaches, with reports suggesting that API attacks and security incidents have risen significantly. This trend highlights the need for robust API security measures to protect businesses and their customers. Notable API breaches in recent years include:
- Yahoo
- Dropbox
- USPS Customer Database
These breaches resulted in the exposure of confidential user information and had significant impacts on the affected entities.
The financial impact of API breaches on businesses can be considerable, with annual global losses reaching up to $75 billion. API breaches can result in substantial financial losses for businesses, affecting not only their reputation but also their bottom line. Strong API security measures are necessary to lessen the risks related to API breaches and safeguard sensitive data against unauthorized access and theft.
Why are APIs Targeted?
APIs, including REST API, are targeted due to their accessibility, the sensitive data they handle, and the potential for attackers to exploit vulnerabilities for unauthorized access or data theft. Because APIs provide a direct route to confidential information, they are often targeted by malicious actors seeking to scrape, distribute, or sell the data on the Dark Web. APIs are known to process sensitive data such as Personally Identifiable Information (PII), financial information, healthcare data, user credentials, and other confidential data, making them attractive targets for malicious actors.
Due to their high accessibility, APIs are a popular target for cyberattacks. APIs are designed to be accessible and usable by multiple applications and users, often exposing them to the internet and making them accessible from anywhere. This increases the attack surface and provides more avenues for attackers to find vulnerabilities and exploit them. Securing APIs is pivotal in safeguarding valuable information and upholding the integrity of the supported systems.
Common API Vulnerabilities
Common API vulnerabilities include broken authentication, insecure direct object references, exposure of sensitive information, and misconfigured CORS, among others. Broken authentication attacks occur when a malicious actor exploits weaknesses in an API’s authentication mechanism, allowing them to impersonate a legitimate user.
An Insecure Direct Object Reference (IDOR) occurs when an API, such as one using OpenID Connect or Simple Object Access Protocol, exposes direct references to internal resources, allowing unauthorized access to data through manipulation of these references. API responses can inadvertently reveal sensitive data, such as user passwords or credit card numbers. This is known as the exposure of sensitive information.
Misconfigured CORS can potentially lead to unauthorized domains making requests, which may result in data breaches and allow attackers to gain unauthorized access.
To guard against these common vulnerabilities, organizations should implement robust API security measures, such as:
- Strong authentication
- Encryption
- Data validation
- Monitoring/logging
API Best Practices
API best practices include:
- Implementing strong authentication and authorization
- Using encryption
- Validating data
- Monitoring and logging
- Regularly updating and patching vulnerabilities
- Deploy bot detection
Strong authentication and authorization mechanisms help protect against unauthorized access to APIs and ensure the confidentiality and integrity of sensitive data. Encryption provides an added layer of security by ensuring that data transmitted between two endpoints remains confidential and tamper-proof.
Data validation helps prevent malicious data from being injected into APIs and causing security breaches. Monitoring and logging activities provide insights into API usage and potential security issues, allowing organizations to quickly detect and respond to threats. Regularly updating and patching vulnerabilities ensures that APIs remain secure against new and emerging threats. Organizations can protect their APIs and preserve user and customer trust by adhering to these best practices.
How to Secure API Calls
Securing API calls involves using the following techniques:
- SSL/TLS encryption: a security protocol used to ensure data confidentiality and integrity when transmitted between two endpoints.
- Implementing rate limiting: a technique used to prevent API abuse and DoS attacks by restricting the number of requests that can be made to an API within a predetermined time frame.
- Employing API gateways: a centralized point for managing and securing API traffic, providing features such as authentication, authorization, and request/response transformation.
- Using web application firewalls: a security measure that protects against malicious traffic by filtering and monitoring HTTP requests.
By implementing these techniques, you can enhance the security of your API calls and effectively gain access to the protected resources.
API gateways function as an API gateway, acting as a “gatekeeper” between the client and the API, filtering out and blocking any suspicious requests before they reach their destination. By implementing access control measures such as web application firewalls, organizations can monitor and filter incoming traffic to a web application, providing an additional layer of security against malicious traffic. This way, they can secure their API calls effectively and shield their APIs from potential threats.
How Kasada Protects Enterprise APIs

Kasada’s layered and holistic defense functions differently, takes the fight to the bots – and exhausts them. Without informing attackers, Kasada’s proof of work challenge exponentially increases the difficulty level along with the number of abusive requests over time. Put simply, it saps adversaries’ resources and makes them work harder. It erodes the ROI of the attack. The results Kasada’s customers see:
- Immediate neutralization of the initial API attack
- Prevention of replay attacks
- Deterrence of future attacks to APIs, apps, and site
When you make attacks too expensive, attackers look elsewhere. When threats can’t retool, they aren’t threats at all. That’s Kasada’s approach: experts in detecting automation with an unmatched knowledge of adversarial techniques – a team and technology that takes the work to you.
How Kasada Stands Out
The Kasada difference:
- Enduring protection: Defeat adversaries with a platform that’s frustrating, time-consuming, and expensive to attack.
- Decisive Defense: No management, rule updates, or decisions to make. Simplify your life.
- Happy Users: Hidden challenges mean zero friction and exceptional user experiences.
- Caring Team: Kasada gives you a team, not just a tool. We’re accountable for stopping the bots.
Organizations can effectively shield their APIs from automated threats and ensure the safety and integrity of their systems and sensitive data by employing Kasada API Protection.
Use Cases
Kasada API Protection is highly versatile, catering to a range of use cases. It ensures the security of customer data by:
- Blocking automation used to launch attacks
- Providing web and API protection against potential threats
- Safeguarding sensitive information from scraping and account takeover attacks
It also helps protect against account takeover attempts by detecting and blocking adversaries who are attempting to take over user accounts at scale to commit acts of fraud.
Kasada API Protection is frequently utilized in industries and fields that depend on APIs for their web applications, including:
- eCommerce & Retail
- Energy & Utilities
- FinTech & Financial Services
- Internet & SaaS
- Travel & Hospitality
- Media, Entertainment, & Gaming
Organizations across different sectors can effectively safeguard their APIs and defend their valuable assets against automated threats and online fraud by deploying Kasada API Protection.
Key Benefits
The key benefits of using Kasada API Protection include enhanced API security, reduced risk of data breaches, and increased customer trust in the organization’s security measures. Kasada API Protection, offering real-time protection against automated attacks, aids in defending APIs against typical web-based attacks and prevents bots from overloading APIs to secure unauthorized access or perpetrate fraud. This proactive approach to security reflects a commitment to safeguarding customer data and maintaining a secure environment, which consequently builds trust and confidence in the organization’s security measures.
Moreover, Kasada API Protection offers the following benefits:
- Mitigates the risk of API breaches by preventing unauthorized access to APIs and safeguarding against malicious automation attacks
- Helps secure API endpoints and decreases the likelihood of API breaches
- Bolsters organizations’ security posture and lessens the risk of data breaches
- Safeguards valuable assets
Implementing Kasada API Protection can help organizations protect their APIs and ensure the security of their valuable assets.
Summary
In conclusion, the importance of API security cannot be overstated in today’s digital landscape. With the rise of API breaches and the sensitive data at stake, organizations must implement robust security measures to protect their APIs. This blog post has explored the world of API security, discussing common vulnerabilities, best practices, and how solutions like Kasada API Protection can help safeguard your APIs. By implementing strong API security measures, organizations can ensure the security and integrity of their systems and sensitive data, ultimately protecting their valuable assets and maintaining the trust of their users and customers. Contact Kasada today to get started.
Frequently Asked Questions
What is an example of API security?
API security involves protecting against malicious attacks such as SQL injection, XSS, and CSRF which can compromise the data transmitted through an API.
How can I secure my API calls?
To secure API calls, use SSL/TLS encryption, implement rate limiting, use an API gateway, and employ a web application firewall.
In which industries or fields is Kasada API protection commonly employed?
Kasada API Protection is commonly used in industries such as eCommerce and retail, utilities, FinTech, internet and SaaS, travel & hospitality, media, entertainment, and gaming.