Headaches for the holidays… thanks to Grinch Bots
Kasada’s Threat Intelligence Team has prepared key insights observed within Kasada’s eCommerce traffic this holiday season.
To no one’s surprise, bots are on the naughty list again this holiday season. We’ve observed a 10x increase in malicious login attempts during the period between Black Friday and Cyber Monday, a strong increase of gift card fraud due to the higher demand for them this year (as a result of the supply chain shortage), and discovered a new sophisticated Grinch Bot used to score goods during holiday sales more successfully than previously seen. Read on to get the full picture of how bad bots are impacting holiday shopping once again.
Holiday shopping is stretching the season – and so are the bots
There have been numerous articles summarizing the overall traffic levels of shoppers during cyber week. For example, according to Fastly, Black Friday was the highest traffic shopping day, with peaks upwards of 40% higher than Thanksgiving and 5% higher than Cyber Monday. Traffic grew as much as 27% ahead of the holiday weekend as compared earlier in the month. eMarketer concluded that the holiday season is stretching out and flattening out, with 19 days this holiday season where eCommerce sales surpassed $3 billion, versus just five days a year ago.
Similar to these other reports, Kasada has also seen the “stretching out” of holiday shopping, as the average daily eCommerce traffic amongst the Cyber Five period—Thanksgiving through Cyber Monday— didn’t vary as much as in prior years. For example, average daily traffic on Black Friday was only 21% higher than the day prior — Thanksgiving. In addition, unlike previous years, heightened bad bot activity began to be observed as early as October, likely as a result of the expected supply chain delays, and the overall increase in online shopping over the past 18-months.
The Kasada Threat Intelligence Team has put together the top online shopping trends related to bad bot activity as seen across our eCommerce customers, put into context by these overall online shopping trends. Kasada currently protects more than $20 billion in eCommerce traffic annually, $10 billion in gift cards, and hundreds of millions of account logins.
Cyber week is a western trend, even amongst botters
During the period between Black Friday and Cyber Monday, we saw the majority of bad bots coming from the USA, followed closely by Australia and the United Kingdom. This year China is of particular interest as it is usually near the top of any botting activity we observe – and it wasn’t during this time period. This suggests that post-Thanksgiving holiday sales are more of a western trend, even amongst botters.
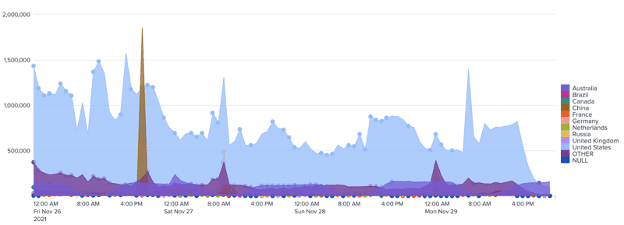
Kasada continues to observe the use of residential proxy networks to hide their bots within seemingly legitimate traffic. Within the United States, especially, bots are attempting to purchase IP addresses that are specific to a retailer’s historical traffic, making it especially difficult for eCommerce providers to distinguish between good and bad traffic.
Online Fraud
4x increase in automated gift card cracking attempts
Similar to how human traffic grew ahead of the Cyber Five period, Kasada saw a growth in online gift card fraud attempts as the holiday season approached. We attribute this to the current “everything shortage” that resulted from the global supply chain issues. This shortage of goods has incentivized bot users to scoop up what in-demand items there were remaining in stock, to resell on secondary marketplaces at large markups, forcing consumers to turn their attention to gift cards. Gift cards are being purchased at a higher rate than ever before, as they can serve as a stopgap for consumers who encounter empty shelves.
Recent research from the cybersecurity research team at Kasada found that automated gift card balance lookups have increased 4x over the past two months. This is a key indicator that fraudsters are using bots to identify and steal gift card balances. In addition, Kasada has seen a rise in stolen gift cards being sold at a discount on the open Internet. In prior years, this type of activity was usually conducted behind closed doors or on the darkweb.
10x increase in malicious login attempts
The Kasada Threat Intelligence Team has identified a 10x increase in malicious login attempts due to credential stuffing during the period between Black Friday and Cyber Monday, compared to the prior weeks in November.
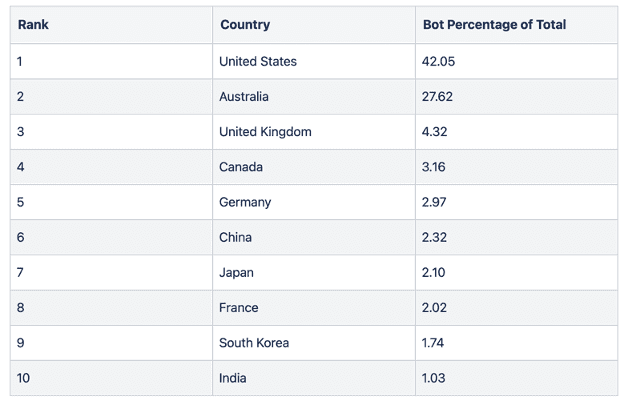
Bad bot logins by country (Eastern US Time)
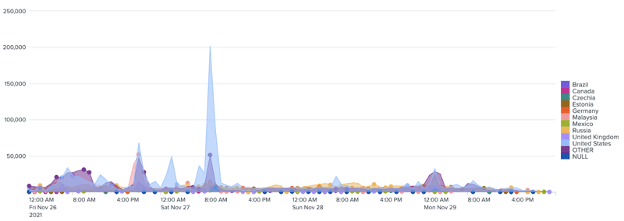
These automated login attempts are most likely conducted to sell stolen account details, which are used for credit card washing, loyalty and reward points draining, and other forms of fraudulent activity. This year we saw the majority of credential stuffing occur on Black Friday and into the early hours of Saturday morning.
Hype Drop Sales
AIO Breeds a More Effective and Efficient Grinch Bot
Hype sales incentivize customers to buy products at a specific time and date. They are designed to increase demand for whatever is being sold-concert tickets, sneakers, PS5s, etc. They also offer a great opportunity for bot operators who exploit these situations to purchase hyped inventory faster than any human can.
Similar to prior years, some of the most sophisticated botting activity occurs during coveted hype drops, where high-demand and limited edition goods are released. Kasada saw a heightened use of all-in-one bots (AIO), like Stellar AIO, which automate the scanning and checkout process for hot items such as electronics.
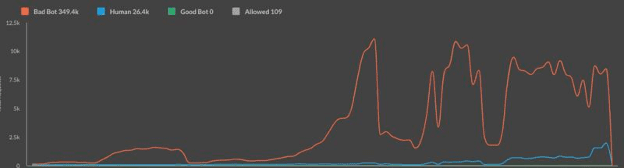
Restock electronics drop: The above image shows that over the course of several minutes, bad bot requests exceeded those from humans by more than 13x. The vast majority of the bad bot requests were made by a Grinch Bot variant which we call “request bots”. Request bots are issued via an API and were successful at bypassing the legacy anti-bot provider that was deployed at the edge, in-front of Kasada’s defense service. Had Kasada not been deployed as an additional layer of defense, more than 90% of these requests would have gotten into the customer’s infrastructure to scan for inventory, add to cart, and automate checkout.
These new request bots have quickly become the de-facto method used for premium hype sales. The percentage of request bots that made up overall traffic during the above hype sale spiked from 0% just prior to the start of the sale, to as much as 99% of all traffic throughout the duration of the hype sale itself. Once the inventory was gone, the request bots essentially disappeared once again until the next drop.
Kasada threat research analyzed the composition of these request bots and determined their use for hype sales is particularly effective due to their (a) lightweight compute requirements, making them especially economical and scalable and (b) their use of fraudulently generated or stolen telemetry data to bypass a multitude of anti-bot providers.
Overall, the two botting trends that have dramatically increased in 2021 for hype sale retailers are the following:
- Request bots – non-browser based scripts that generate and maintain valid human tokens by replaying the expected human telemetry to an anti-bot provider
- Headless browsers – heavily customized versions of the leading automation frameworks, such as Puppeteer Stealth and Playwright – including CAPTCHA bypass
Summary
It was especially difficult to keep ahead of the bots during this year’s Cyber Five and the months leading-up to it. Bots were used not only to automate the purchasing of in-demand goods, but also to commit online fraud by using automation to crack gift card codes and to take over accounts with stolen or purchased credentials. Malicious automation continues to evolve with very sophisticated customized open source tools, residential proxy networks, and request bots. By using APIs to replay expected human telemetry, bots can trick most legacy anti-bot systems that are left vulnerable to such methods.
How’d you fare during Black Friday and Cyber Monday?
If the past year and a half has taught us anything, it’s you’re ready until you’re not. Retailers fortified their online businesses in anticipation of peak shopping season, but for many, it still wasn’t enough. We’ve had numerous customers realize the ineffectiveness of their previous anti-bot solution only after seeing peak holiday season traffic.
Bot operators have figured out how to work their way around the defenses that are unable to keep up with modern trends. This correlates with the findings of our 2021 State of Bot Mitigation Survey, where 85% of respondents using bot management solutions said their solution lost its effectiveness within 12 months of deployment.
If you’re not sure if bad bots are a problem for your company, you can quickly test your site here to see which bot threats you’re unable to detect and stop.
We’d love to show you more of our threat intelligence and our modern approach to bot mitigation as we protect $20B in eCommerce revenue from some of the most complex bots – likely the same ones that are hitting your digital channels.
Special thanks to James Schubach and Nick Rieniets for their thoughtful analysis of this year’s holiday shopping activity.



