One of the best ways to protect against your enemy is to understand their strategies and tactics and proactively prepare your response. In other words: know your adversary. This post explores the open source dev tools and antidetect browsers that malicious actors use to automate their cyber attacks.
Two Primary Categories of Hack Tools
The rise of automation frameworks have helped attackers gain an advantage in the bot mitigation wars, and why not? – these advanced tools and techniques are inexpensive, easy-to-use, highly scalable, and unfortunately, quite effective.
Generally speaking, there are two types of tools that adversaries use to automate bot attacks:
- Legitimate automation tools that are repurposed for nefarious uses; and
- Purpose-built fraud toolkits.
Let’s take a closer look at each.
Legitimate Tools Repurposed for Fraud
Some tools originally designed for web developers – such as browser automation toolkits like Puppeteer from Google and Playwright from Microsoft (among others) – have been adapted for illegitimate purposes.
While it’s great that tools like Puppeteer exist to automate testing with headless browsers (browsers without graphical UIs), their original purpose has now been subverted. It makes sense for attackers to do this: these tools provide a powerful and flexible capability to automate browsers in a way that is undetectable to many bot mitigation providers.
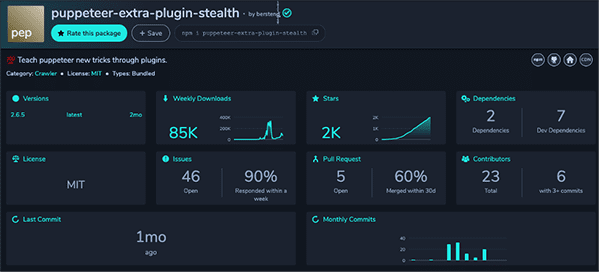
Puppeteer has become highly popular as a headless Chrome Devtest tool since the availability of v1.0 from Google in 2018. Unfortunately, Puppeteer Stealth Mode plugin has also become highly popular, when added to Puppeteer, as a method to mimic human behavior and fly below the radar of most bot detection tools.
What does that mean, exactly? Well, if you do not have a client-side inspection method (like Kasada), there is simply no way to differentiate between “A user + Chrome” versus “A user + Puppeteer + Chromium.” Your existing security solutions cannot differentiate between the two, leaving you vulnerable to automated bot attacks. Bot operators work at scale to create an enormous amount of headless browsers to simulate human actions (mouse control, scrolling, click patterns) which leads to expensive fake traffic, fake account creation, click fraud, and DoS attacks, among other unfortunate outcomes.
Homegrown Tools, Such as Purpose-Built Fraud Tools
A prime example of a purpose-built fraud tool is an antidetect browser, most commonly developed in Russia. Antidetect browsers are marketed as privacy tools and use standard browser engines with harvested digital fingerprints from legitimate browser sessions. This allows adversaries to randomize all aspects of the browser presentation, which makes them undetectable by most bot detection solutions. Examples of antidetect browsers include Linken Sphere, Antbrowser, Aezakmi, and Indigo (multi-login).
The Nuances of Different Browser Engines
Understanding the nuance between different browser engines is critical to understanding why antidetect browsers exist in the first place. Early versions of bot detection that leverage standard browser fingerprinting can detect the difference between the browser engines via JavaScript inspection.
Examples of browser engine differences:
- Only Internet Explorer has support for ActiveX
- Chrome does not support MathML
Note: This is an excellent resource for understanding differences in browser engines.
The primary objective of an antidetect browser is to patch the underlying browser so it presents consistently when inspected. Examples are a)ensuring that hardware matches the userAgent profile or b) ensuring that navigator objects match the location (e.g., timezone, languages, fonts, plugins, etc.). Antidetect browsers use a range of techniques to achieve this, ranging from customizing browser source code to overwriting the values on the page with JavaScript.
The bottom line: Adversaries use both types of tools together with advanced techniques to mimic legitimate user behavior to conduct low and slow automated attacks on web applications.
Preferred Tactics and Techniques
Over the years, we’ve seen many different types of bot attacks and have witnessed their evolution in terms of sophistication and ability to evade detection.
Here are six tactics that stealthy attackers typically employ to fly under the radar:
- A sophisticated automation framework that translates their scripted attack into a series of browser-based requests.
- Proxy rotation services with residential proxy networks to deliver single requests per IP from a region closest to their target.
- Randomizing the request headers to ensure no signals are provided in the data.
- Randomizing the time sequence between requests.
- Matching the velocity of requests to the daily patterns of the target’s legitimate customers.
- Matching the browser presentation layer (DOM) to the request header patterns.
We believe the only way to stay ahead of adversaries is through deeply understanding these advanced tools and techniques to predict, prepare, and defend against what they will do next.
What Can You Do About These DevTools and Antidetect Browsers?
Because the data available for inspection (such as network, headers, time, presentation) is being manipulated by the attacker, what looks like a regular request from a Chrome browser on an iPhone from a local ISP, for example, is actually something entirely different.
Advanced attackers leveraging automation tools can only be stopped through sophisticated bot management that goes beyond traditional methods such as blocking IP addresses, inspecting userAgent profiles, and searching for anomalous traffic patterns. Specifically, what we call “client-side interrogation” which is able to detect the automation frameworks and associated plugins used to mimic human behavior. Without access to client-side interrogation data, there is nothing to tie the individual attack requests together to understand what is really happening.
How Kasada Detects and Stops Automated Attacks Never Seen Before
Kasada is an effective bot detection and mitigation solution that works to identify automated threats and subsequently stop them – before the first request. Kasada accurately detects and defends against bot attacks never seen before across web, mobile, and API channels. Kasada’s advanced client-side inspection method enables customers to detect the hidden threats posed by automated toolkits (regardless of whether they are legitimate out-of-the-box tools repurposed for fraud or homegrown fraud tools). Thus, the invisible threat posed by Puppeteer stealth or an antidetect browser is automatically exposed and stopped in real time.
We can do that because Kasada exposes a new dimension of data for our customers to leverage when protecting against bots. We interact, inspect, and challenge the client (browser / mobile / bot) that is sending the request to their applications. Put differently, we take up residence inside the bot. This inside-out view exposes an entirely different perspective, enabling us to see behind the requests, and dynamically interact with – and challenge – the attackers’ platform. Coupled with our data analytics engine and a range of mitigative actions, the Kasada platform provides a more modern approach to stopping how bots operators are conducting attacks nowadays.
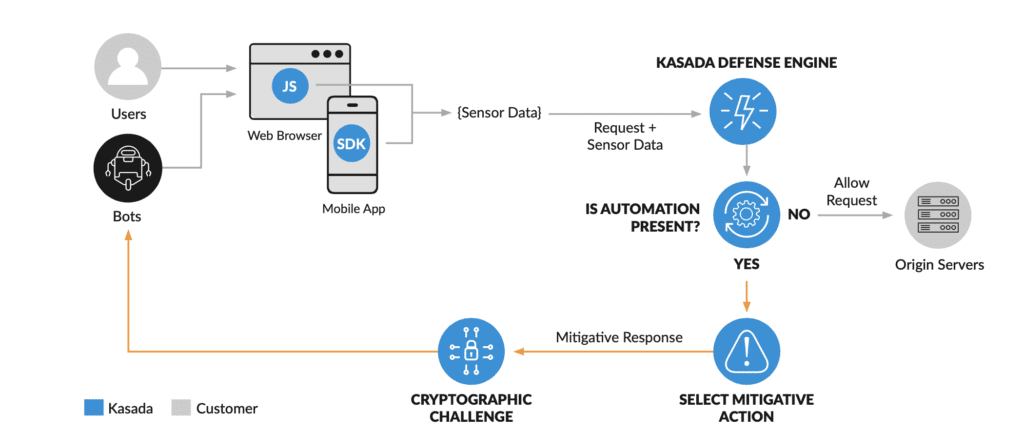
The result? Your security operations team can proactively respond to fraudulent activity before the attack even begins. By leveraging the additional (client-side) dimension of data that Kasada provides, you can confirm the authenticity (or lack thereof) of your web traffic. That’s because this approach allows you to differentiate between a legitimate browser and a manipulated, patched automated browser. You’ll be able to see the process of browser manipulation in a clear and concise way to detect fraudulent, unauthentic traffic.
If you don’t have visibility into what your adversaries are doing, it’s impossible to stay ahead. You can easily achieve that level of visibility with Kasada to stop sophisticated bot attacks that others can’t.
To see how bot operators are using the latest automation tools to work around your existing web and mobile defenses, request a free threat briefing and demo today.



